SY0-701 Online Practice Questions and Answers
Several employees received a fraudulent text message from someone claiming to be the Chief Executive Officer (CEO). The message stated: "I'm in an airport right now with no access to email. I need you to buy gift cards for employee recognition awards. Please send the gift cards to following email address."
Which of the following are the best responses to this situation? (Choose two).
A. Cancel current employee recognition gift cards.
B. Add a smishing exercise to the annual company training.
C. Issue a general email warning to the company.
D. Have the CEO change phone numbers.
E. Conduct a forensic investigation on the CEO's phone.
F. Implement mobile device management.
Which of the following should a systems administrator use to ensure an easy deployment of resources within the cloud provider?
A. Software as a service
B. Infrastructure as code
C. Internet of Things
D. Software-defined networking
A client demands at least 99.99% uptime from a service provider's hosted security services. Which of the following documents includes the information the service provider should return to the client?
A. MOA
B. SOW
C. MOU
D. SLA
A user is attempting to navigate to a website from inside the company network using a desktop. When the user types in the URL. https://www.site.com, the user is presented with a certificate mismatch warning from the browser. The user does not receive a warning when visiting http://www.anothersite.com. Which of the following describes this attack?
A. On-path
B. Domain hijacking
C. DNS poisoning
D. Evil twin
A security administrator recently reset local passwords and the following values were recorded in the system:
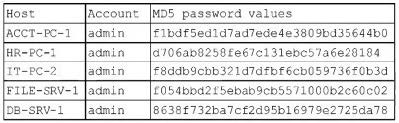
Which of the following is the security administrator most likely protecting against?
A. Account sharing
B. Weak password complexity
C. Pass-the-hash attacks
D. Password compromise
During a penetration test, a vendor attempts to enter an unauthorized area using an access badge. Which of the following types of tests does this represent?
A. Defensive
B. Passive
C. Offensive
D. Physical
The security operations center is researching an event concerning a suspicious IP address. A security analyst looks at the following event logs and discovers that a significant portion of the user accounts have experienced faded log-In attempts when authenticating from the same IP address:
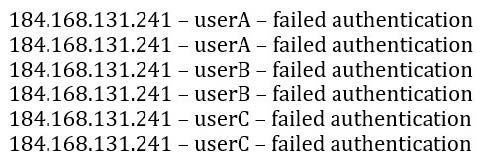
Which of the following most likely describes attack that took place?
A. Spraying
B. Brute-force
C. Dictionary
D. Rainbow table
A security team is setting up a new environment for hosting the organization's on-premises software application as a cloud-based service. Which of the following should the team ensure is in place in order for the organization to follow security best practices?
A. Visualization and isolation of resources
B. Network segmentation
C. Data encryption
D. Strong authentication policies
A security analyst is investigating an application server and discovers that software on the server is behaving abnormally. The software normally runs batch jobs locally and does not generate traffic, but the process is now generating outbound traffic over random high ports. Which of the following vulnerabilities has likely been exploited in this software?
A. Memory injection
B. Race condition
C. Side loading
D. SQL injection
The Chief Information Security Officer (CISO) at a large company would like to gain an understanding of how the company's security policies compare to the requirements imposed by external regulators. Which of the following should the CISO use?
A. Penetration test
B. Internal audit
C. Attestation
D. External examination