SC-100 Online Practice Questions and Answers
You have a Microsoft 365 E5 subscription and an Azure subscription.
You are designing a Microsoft deployment.
You need to recommend a solution for the security operations team. The solution must include custom views and a dashboard for analyzing security events.
What should you recommend using in Microsoft Sentinel?
A. playbooks
B. workbooks
C. notebooks
D. threat intelligence
Your company has an office in Seattle.
The company has two Azure virtual machine scales sets hosted on different virtual networks.
The company plans to contract developers in India.
You need to recommend a solution to provide the developers with the ability to connect to the virtual machines over SSL from the Azure portal. The solution must meet the following requirements:
1.
Prevent exposing the public IP addresses of the virtual machines.
2.
Provide the ability to connect without using a VPN.
3.
Minimize costs.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. Create a hub and spoke network by using virtual network peering.
B. Deploy Azure Bastion to each virtual network.
C. Enable just-in-time VM access on the virtual machines.
D. Create NAT rules and network rules in Azure Firewall.
E. Deploy Azure Bastion to one virtual network.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
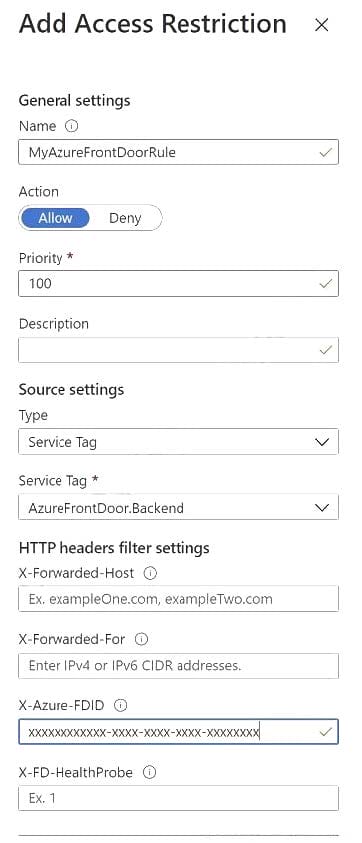
You are designing a security strategy for providing access to Azure App Service web apps through an Azure Front Door instance.
You need to recommend a solution to ensure that the web apps only allow access through the Front Door instance.
Solution: You recommend access restrictions to allow traffic from the backend IP address of the Front Door instance.
Does this meet the goal?
A. Yes
B. No
You have a customer that has a Microsoft 365 subscription and an Azure subscription.
The customer has devices that run either Windows, iOS, Android, or macOS. The Windows devices are deployed on-premises and in Azure.
You need to design a security solution to assess whether all the devices meet the customer's compliance rules.
What should you include in the solution?
A. Microsoft Defender for Endpoint
B. Microsoft Endpoint Manager
C. Microsoft Information Protection
D. Microsoft Sentinel
You have an on-premises network that has several legacy applications. The applications perform LDAP queries against an existing directory service.
You are migrating the on- premises infrastructure to a cloud-only infrastructure.
You need to recommend an identity solution for the infrastructure that supports the legacy applications. The solution must minimize the administrative effort to maintain the infrastructure.
Which identity service should you include in the recommendation?
A. Azure AD B2C
B. Azure Active Directory Domain Services (Azure AD DS)
C. Azure AD
D. Active Directory Domain Services (AD DS)
Your company develops several applications that are accessed as custom enterprise applications in Azure AD.
You need to recommend a solution to prevent users on a specific list of countries from connecting to the applications.
What should you include in the recommendation?
A. activity policies in Microsoft Defender for Cloud Apps
B. sign-in risk policies in Azure AD Identity Protection
C. Azure AD Conditional Access policies
D. device compliance policies in Microsoft Endpoint Manager
E. user risk policies in Azure AD Identity Protection
You have a Microsoft 365 subscription.
You need to design a solution to block file downloads from Microsoft SharePoint Online by authenticated users on unmanaged devices.
Which two services should you include in the solution? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. Azure AD Conditional Access
B. Azure Data Catalog
C. Microsoft Purview Information Protection
D. Azure AD Application Proxy
E. Microsoft Defender for Cloud Apps
You have an operational model based on the Microsoft Cloud Adoption Framework for Azure.
You need to recommend a solution that focuses on cloud-centric control areas to protect resources such as endpoints, databases, files, and storage accounts.
What should you include in the recommendation?
A. business resilience
B. modem access control
C. network isolation
D. security baselines in the Microsoft Cloud Security Benchmark
You have a Microsoft 365 tenant. Your company uses a third-party software as a service (SaaS) app named App1. App1 supports authenticating users by using Azure AD credentials.
You need to recommend a solution to enable users to authenticate to App1 by using their Azure AD credentials.
What should you include in the recommendation?
A. Azure AD Application Proxy
B. Azure AD B2C
C. an Azure AD enterprise application
D. a relying party trust in Active Directory Federation Services (AD FS)
You have an Azure AD tenant that syncs with an Active Directory Domain Services (AD DS) domain.
You are designing an Azure DevOps solution to deploy applications to an Azure subscription by using continuous integration and continuous deployment (CI/CD) pipelines.
You need to recommend which types of identities to use for the deployment credentials of the service connection. The solution must follow DevSecOps best practices from the Microsoft Cloud Adoption Framework for Azure.
What should you recommend?
A. a managed identity in Azure
B. an Azure AD user account that has role assignments in Azure AD Privileged Identity Management (PIM)
C. a group managed service account (gMSA)
D. an Azure AD user account that has a password stored in Azure Key Vault