CISSP-2018 Online Practice Questions and Answers
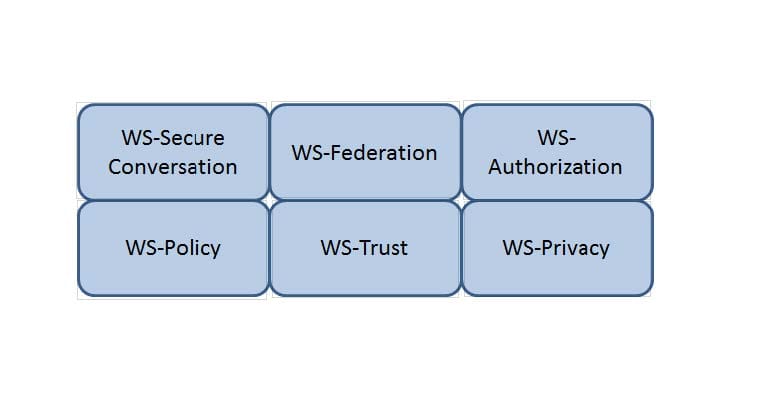
HOTSPOT
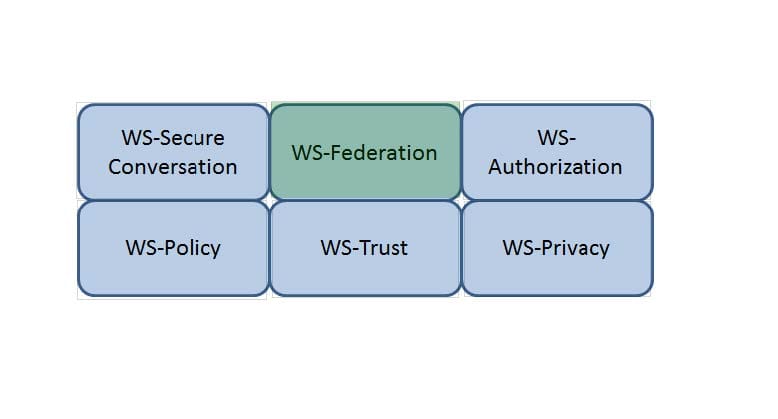
Which Web Services Security (WS-Security) specification maintains a single authenticated identity across multiple dissimilar environments? Click on the correct specification in the image below.
Hot Area:
HOTSPOT
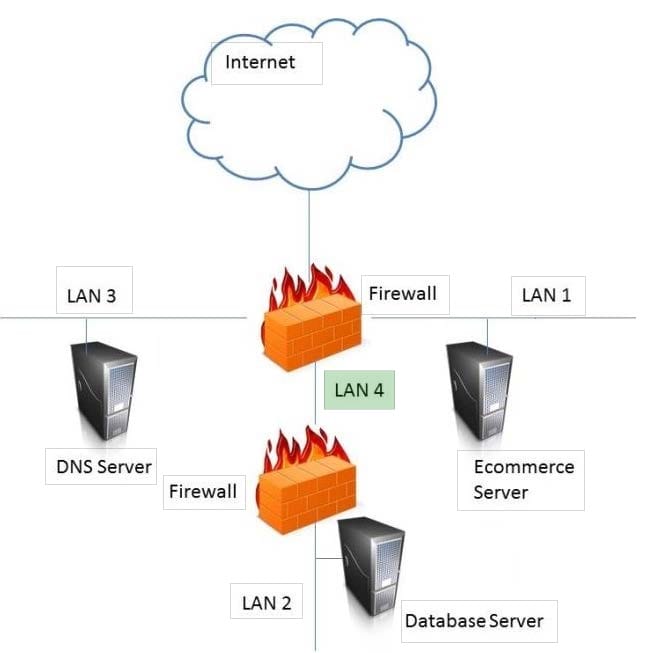
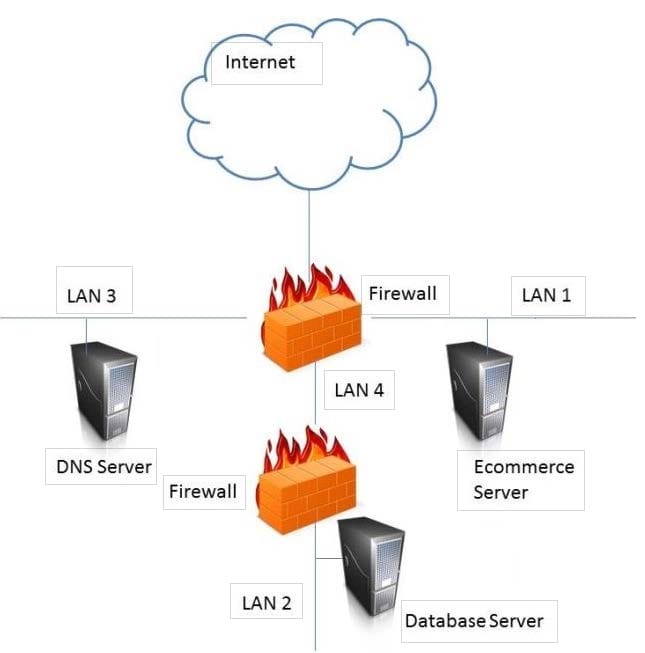
In the network design below, where is the MOST secure Local Area Network (LAN) segment to deploy a Wireless Access Point (WAP) that provides contractors access to the Internet and authorized enterprise services?
Hot Area:
DRAG DROP
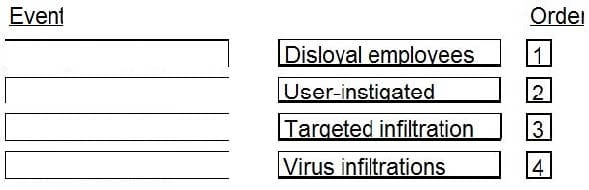
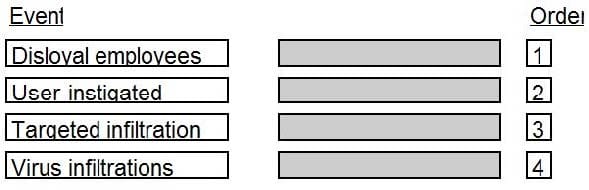
In which order, from MOST to LEAST impacted, does user awareness training reduce the occurrence of the events below?
Select and Place:
DRAG DROP
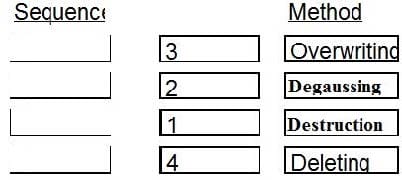
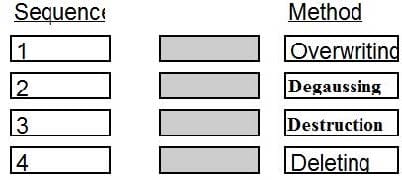
Place in order, from BEST (1) to WORST (4), the following methods to reduce the risk of data remanence on magnetic media.
Select and Place:
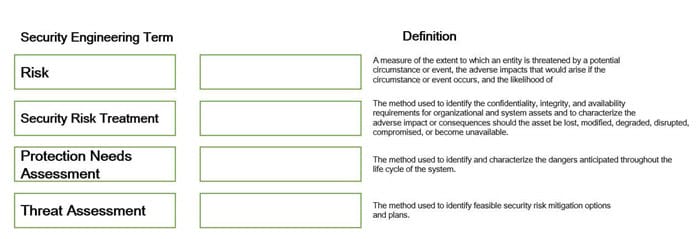
DRAG DROP
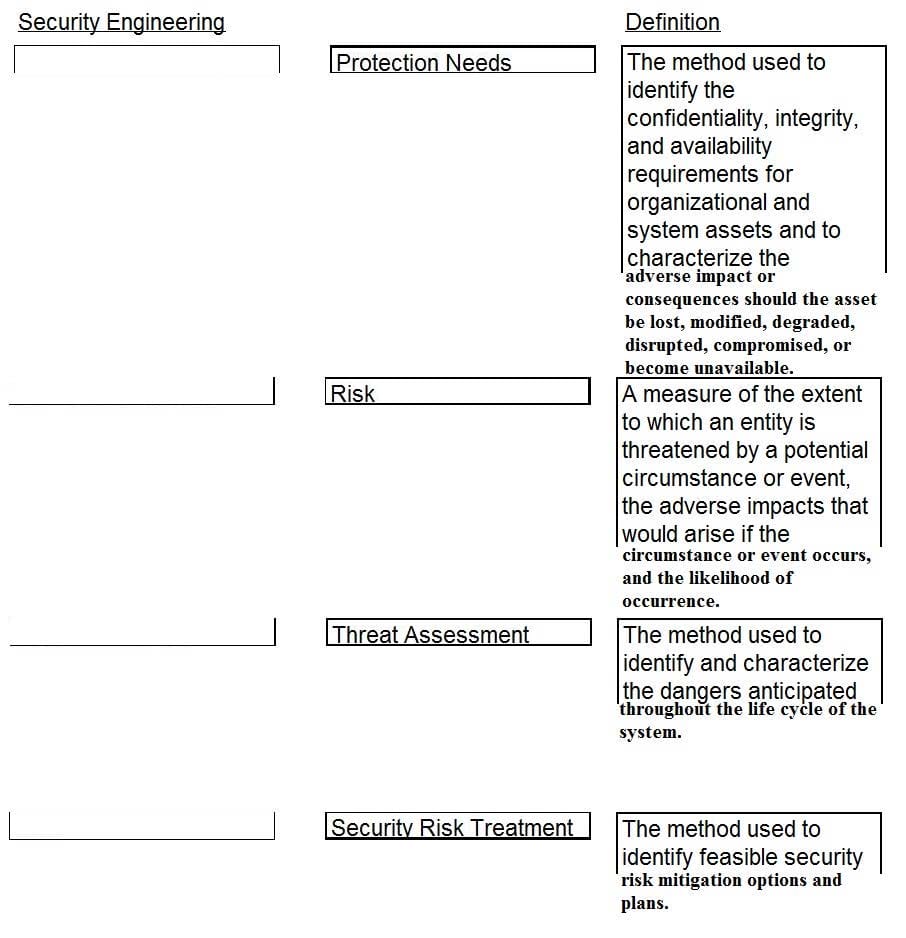
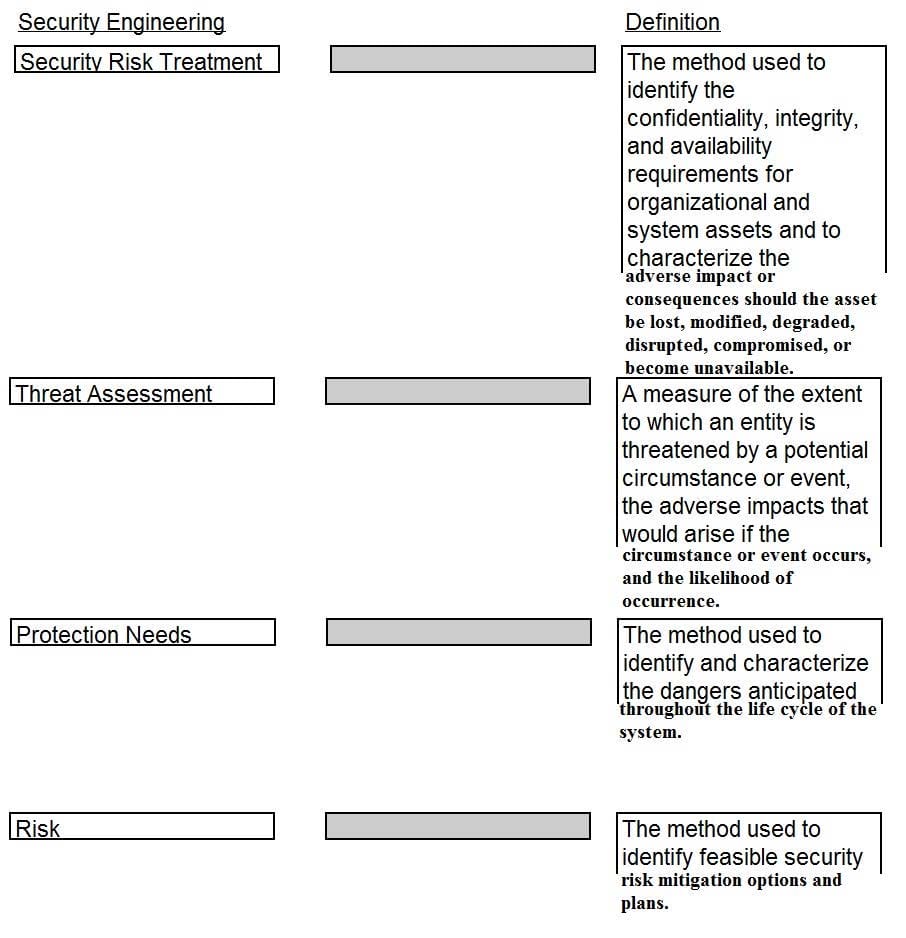
Drag the following Security Engineering terms on the left to the BEST definition on the right.
Select and Place:
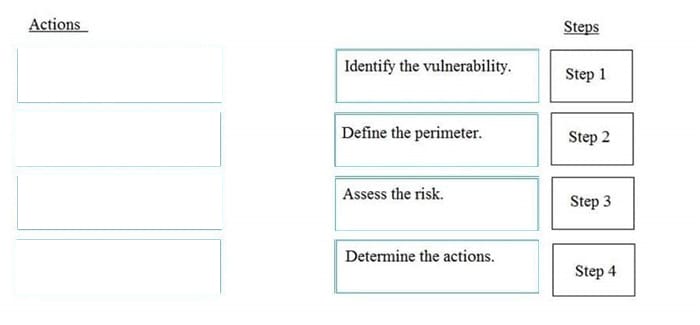
DRAG DROP
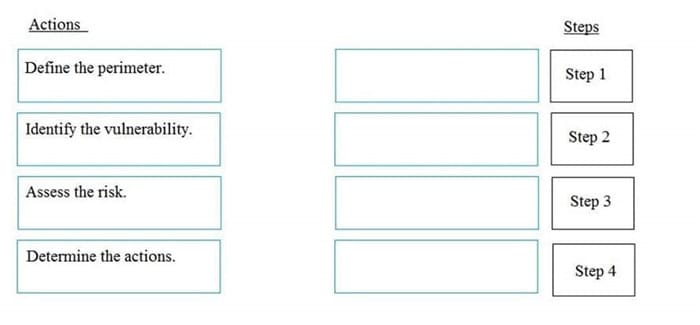
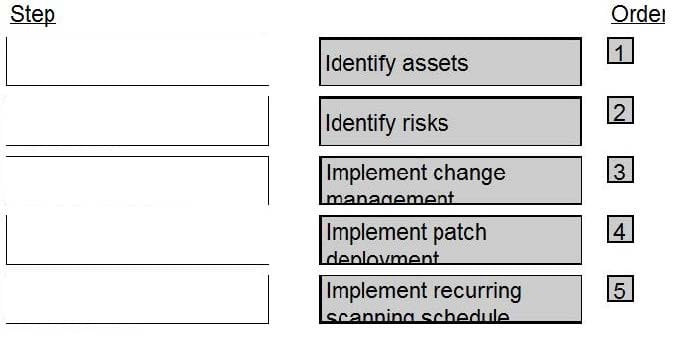
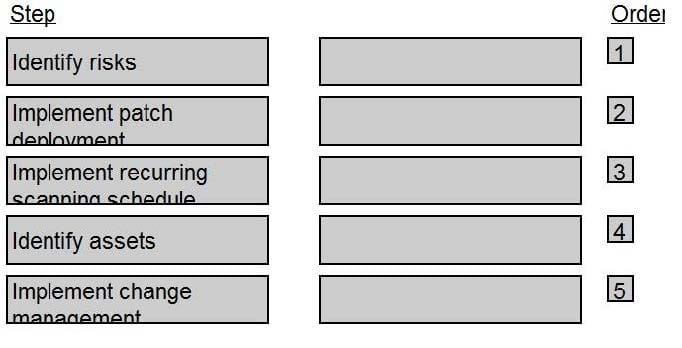
Order the below steps to create an effective vulnerability management process.
Select and Place:
DRAG DROP
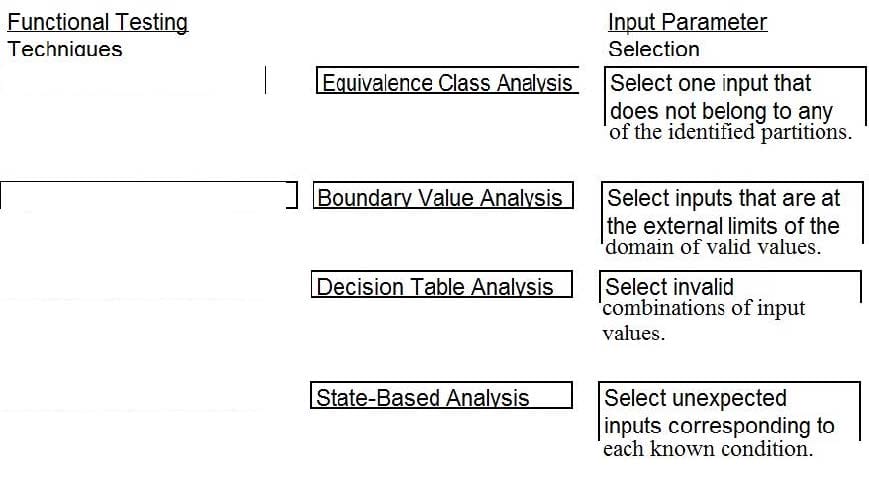
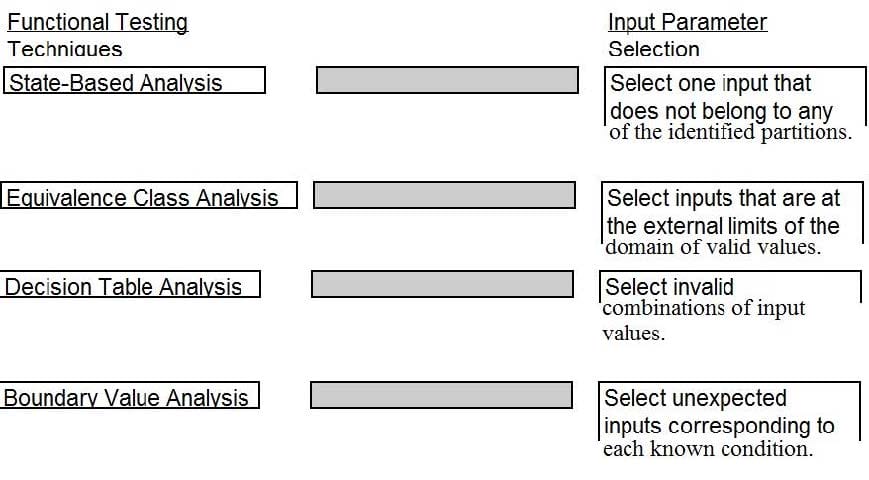
A software security engineer is developing a black box-based test plan that will measure the system's reaction to incorrect or illegal inputs or unexpected operational errors and situations. Match the functional testing techniques on the left with the correct input parameters on the right.
Select and Place:
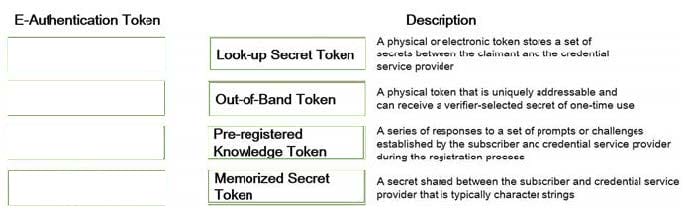
DRAG DROP
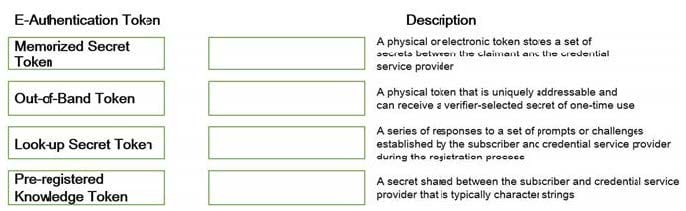
Match the types of e-authentication tokens to their description.
Drag each e-authentication token on the left to its corresponding description on the right.
Select and Place:
DRAG DROP
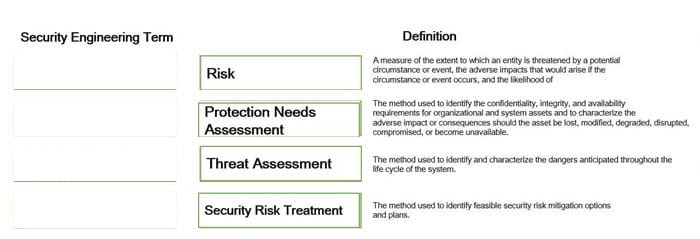
Drag the following Security Engineering terms on the left to the BEST definition on the right.
Select and Place:
DRAG DROP
What is the correct order of steps in an information security assessment?
Place the information security assessment steps on the left next to the numbered boxes on the right in the correct order.
Select and Place: